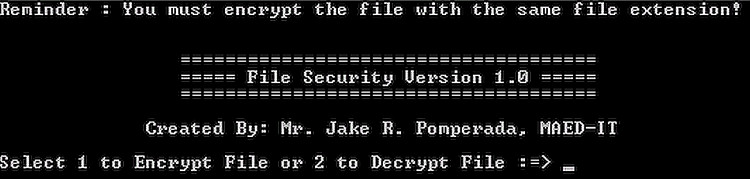
File Security Version 1.0
Submitted by jakerpomperada on Saturday, October 31, 2009 - 10:53.
Language
One of the biggest problem of computer system now a days is computer security to address that problem I develop a simple program I called it File Security Version 1.0 written entirely in C++ . It uses encryption and decryption algortihm to protect file from altering or any modification by intruder or unauthorized users. According to wikipedia.com encryption is the process of transforming information (referred to as plaintext) using an algorithm (called cipher) to make it unreadable to anyone except those possessing special knowledge, usually referred to as a key. The result of the process is encrypted information (in cryptography, referred to as ciphertext). In many contexts, the word encryption also implicitly refers to the reverse process, decryption (e.g. “software for encryption” can typically also perform decryption), to make the encrypted information readable again (i.e. to make it unencrypted).
Encryption has long been used by militaries and governments to facilitate secret communication. Encryption is now commonly used in protecting information within many kinds of civilian systems. For example, in 2007 the U.S. government reported that 71% of companies surveyed utilized encryption for some of their data in transit.[1] Encryption can be used to protect data "at rest", such as files on computers and storage devices (e.g. USB flash drives). In recent years there have been numerous reports of confidential data such as customers' personal records being exposed through loss or theft of laptops or backup drives. Encrypting such files at rest helps protect them should physical security measures fail. Digital rights management systems which prevent unauthorized use or reproduction of copyrighted material and protect software against reverse engineering (see also copy protection) are another somewhat different example of using encryption on data at rest.
Encryption is also used to protect data in transit, for example data being transferred via networks (e.g. the Internet, e-commerce), mobile telephones, wireless microphones, wireless intercom systems, Bluetooth devices and bank automatic teller machines. There have been numerous reports of data in transit being intercepted in recent years.[2] Encrypting data in transit also helps to secure it as it is often difficult to physically secure all access to networks.
Encryption, by itself, can protect the confidentiality of messages, but other techniques are still needed to protect the integrity and authenticity of a message; for example, verification of a message authentication code (MAC) or a digital signature. Standards and cryptographic software and hardware to perform encryption are widely available, but successfully using encryption to ensure security may be a challenging problem. A single slip-up in system design or execution can allow successful attacks. Sometimes an adversary can obtain unencrypted information without directly undoing the encryption. See, e.g., traffic analysis, TEMPEST, or Trojan horse.
One of the earliest public key encryption applications was called Pretty Good Privacy (PGP), according to Paul Rubens. It was written in 1991 by Phil Zimmermann and was purchased by Network Associates (now PGP Corporation) in 1997.
There are a number of reasons why an encryption product may not be suitable in all cases. First, e-mail must be digitally signed at the point it was created to provide non-repudiation for some legal purposes, otherwise the sender could argue that it was tampered with after it left their computer but before it was encrypted at a gateway according to Paul. An encryption product may also not be practical when mobile users need to send e-mail from outside the corporate network.
If you find my work useful send me an email at [email protected]. People here in the Philippines who wish to contact me can reach me in my mobile phone number at 09296768375 and my landline number at +63 (034) 4335081 . Take care always and Happy Programming.
Regards,
Mr. Jake Rodriguez Pomperada, MAED - Instructional Technology
Programmer, Teacher and Computer Techncian
Note: Due to the size or complexity of this submission, the author has submitted it as a .zip file to shorten your download time. After downloading it, you will need a program like Winzip to decompress it.
Virus note: All files are scanned once-a-day by SourceCodester.com for viruses, but new viruses come out every day, so no prevention program can catch 100% of them.
FOR YOUR OWN SAFETY, PLEASE:
1. Re-scan downloaded files using your personal virus checker before using it.
2. NEVER, EVER run compiled files (.exe's, .ocx's, .dll's etc.)--only run source code.