Upload Source
I think you should upload the source code for this program.
I have created a trojan horse before that looks like a sub seven trojan horse. I did it just for fun. I am wondering if I will share it here. I need your opinion before I upload the source code.
This is for educational purpose only and I am not liable for any damages that this program will cause in your system.
The trojan is a kind of tools use for hacking other computer. Of course I did not use this to penetrate other system.
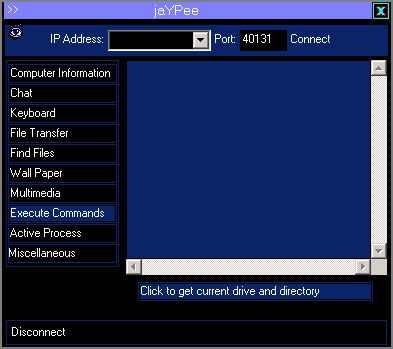
After you run the server program it will simply reside on your computer and will not do anything until the client program connects and send commands like restarting a computer. It can also open/close cd-rom, open application, log keystroke, delete files, etc. in a remote computer.
I don't know if this can help you or just complicate the situation.
My purpose here is to teach you on how to code and do not have an intention to create a malicious software like this. This is an informational only on how to code a client/server architecture.
Here's the screenshot.
Your comments or suggestions is highly appreciated.
Update: You can access the source code at Trojan - Subseven Alike.
I think you should upload the source code for this program.
May be you mean how to download the source code. Here's the link to Trojan Source Code.
I'm saying that it makes me wonder if your ~other~ programs are safe (like the ocx's with the inventory application). They probably are, but it creates a cloud of suspicion. Something to think about...
And what is your suspicion? Did your antivirus detects any malicious code in my ocx?
Look at the quick links to download the source code.
I updated the content above. Download the code on the link.